As Flock continues to battle transparency and expunge the public record, the logs—reduced as they may be—continue to yield insights into the privately-owned and -operated Surveillance-as-a-Service network. The latest: a drug task force out of Brookfield, Missouri (pop. ~4,000) retrieved a vehicle’s location history and accidentally exposed the scale of the Flock network—and, potentially, violated the laws of several states in the process.

flocksafety.com homepage touting 5,000+ and "networks searched" showing 6,385
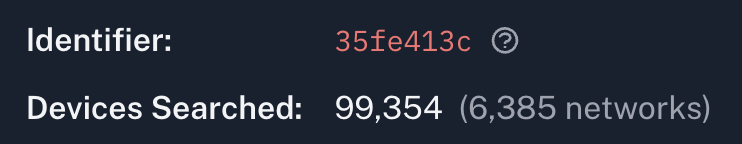
On its website’s main landing page, Flock claims it is “Trusted by 5,000+ law enforcement agencies.” That number roughly lines up with the 5,730 agencies seen in search logs, and the ~6,400 “networks searched” we see in network audit logs.[1]
Brookfield’s “ICE detainer” search, however, reveals a much bigger number: 25,263.
This search was logged twice, once at 04:10:13, and once at 04:10:31:[2]
- Name: “REDACTED”
- Organization: “North MO DTF Brookfield MO PD”
- Networks Searched: 25,263
- Devices Searched: “257,806”
- Time Frame: 10/30/2025, 10:06:10 PM UTC to 10/31/2025, 04:06:10 AM UTC
- License Plate: “REDACTED”
- Reason: “ICE detainer”
- Case #: “643”
- Filters: “REDACTED”
- Search Time: 10/31/2025, 04:10:13 AM UTC
- Type: “lookup”
- Text Prompt: None
- Moderation: An issue was identified that caused the system to initiate unprocessed search activity on a larger set of cameras than intended by the user. No footage or data from these devices was accessed or viewed. The underlying bug has been fixed, and additional safeguards have been implemented to prevent recurrence.
The moderation field, which generally contains only the word allow, and is assumed to be the
outcome of Flock’s AI moderator checking for problematic searches, appears to contain a manually
entered case note instead.[3]
The critical phrase is: “No footage or data from these devices was accessed or viewed.”
This implies that the 257,806 devices across 25,263 networks weren’t supposed to be searched, but they actually do exist and have search and view capabilities.
This is both interesting and problematic. It is interesting because the size of Flock’s network is the subject of some speculation. We can draw inferences from “total devices/networks searched,” but we don’t know what individual agencies searched, or can access.
There are agencies that contractually have no restrictions on which Flock networks or cameras they access, but these agencies don’t appear to conduct searches of significantly more networks or devices than others. It’s possible that, in those cases, Flock only grants access to a subset of its cameras, despite the terms.
Of course, the company treats audit logs—marketed as building community trust through transparency— in much the same way as the CIA treats its “South America” Rolodex.
Still, knowing the background, we can continue inferring based on these new log entries showing 257,806 devices and 25,263 networks. The (plausible) facts:
- More than a quarter million Flock “devices” exist on Flock’s network.
- Because this was a search for a plate, and the note mentions “footage” and “viewing,” all 257,806 “devices” are likely cameras (Falcon, Condor, Wing, etc.).
- There are fewer than 25,263 agencies in the country;[4] the ~5,000–6,000 Flock-using agencies is well-supported.
- Even if the majority of ~6,000 agencies would have multiple networks, it would not come close to the 25,263 number.
The only reasonable conclusion, based on the available information, is that the 25,263 number includes Flock’s retail customers, like Lowe’s, Academy Sports, and FedEx.
But there’s another implication: California, Illinois, and Virginia have enacted laws restricting immigration-related searches of their ALPR data. If Flock’s bug exposed cameras in those states to an “ICE detainer” search—even if, as the company claims, “no footage or data was accessed or viewed”—that’s a potential violation of state law that Flock has disclosed to no one except through a log entry nobody was meant to read.
The fact that these 257,806 devices are collecting over twenty billion plate scans every month is interesting and terrifying in itself, but not a complete shock.
What is more shocking is that once again, Flock’s poor security practices are revealed.
Even assuming the implausible note is true, and these (presumed) retail devices were not searched, the capability is clearly there.
That means Flock’s access control is done through various vendor-managed flags and roles, rather than through secure measures like encryption.
When a retailer or government believes it is sharing “its data” with local police, rather than having Flock register a secure password or encryption key for the local agency, it’s a permission checkbox: “go ahead and disclose it, Flock.”
That is not control, and it’s not security.[5] It’s trusting a vendor that has shown it can’t be trusted. It leaves the door wide open to unauthorized access, uncontrolled dissemination, and software bugs.
In all likelihood, Flock did not proactively disclose this incident or the details of its investigation and remediation steps.[6] Instead, it chose to edit the “immutable” logs and updated the “moderation” field. The logs don’t indicate the (supposedly) intended search scope, nor is there any way to verify if any other edits were made.
Flock’s customers—whether private retailers or California cops—simply have no way of knowing if this search touched or disclosed data from “their” networks.
All we have is a statement hidden in a log file that nobody reads, in a field not intended for it, where the company assures us, without providing evidence, that multiple states’ prohibitions on immigration-related searches were not violated through this search.
What’s more, Flock, a single private corporation, now operates a camera for every 1,000 American adults.
The company wants there to be many more, all built on the same fundamentally flawed security framework: “trust Flock.”
This search demonstrates—again—why we can’t allow that.
Some customers appear to have multiple networks, separated by product type (e.g. one network for “Falcon” and one network for “Raven” voice detectors). ↩︎
These times differ fairly significantly from the search window time of 04:06:26. This could indicate the user was slow to complete the search form, or may indicate system issues. ↩︎
Again demonstrating the mutability of audit logs. ↩︎
17,541 in 2018, according to the Bureau of Labor Statistics ↩︎
It’s also expressly prohibited by CJISSECPOL. ↩︎
If it did, the disclosure should be available via open records request from any Flock-using agency. If you have information that Flock took proactive steps, reach out. ↩︎