The Platform: Flock Safety Is Running on Promises, Not Policy
Flock Safety's three campaign promises — local control, no federal access, no employee access — are contradicted by Dunwoody PD audit logs, an FBI criminal complaint, and a Flock training video recorded on a live police account.
Flock Safety has been running on the same platform for years. Not a technology platform — a political one. Three promises, repeated at every city council meeting, embedded in every sales pitch, printed on every FAQ page. The kind of promises a candidate makes when they need the room to stop asking questions and start signing contracts.
Audit logs and user exports from a mid-sized Georgia suburb, a Loom training video recorded on a live account in Washington state, and a federal criminal complaint filed in the Southern District of Texas all tell a different story than the one Flock tells on the campaign trail.
The Stump Speech
Flock’s Privacy & Ethics page states that “only your agency decides who to share data with, not Flock.” Their FAQ goes further: “Nobody from Flock Safety is accessing or monitoring your footage.”
@Flock Safety — Privacy & Ethics
A January 2026 blog post insists that “ICE does not have direct access to Flock cameras, systems, or data.” It lists a number of “pilot projects,” including a “CBP Pilot: May 9, 2025 to August 24, 2025.” These pilot projects “effectively enabl[ed prospective customers] to test the product before committing to it.” In other words, they got access.
Flock CEO Garrett Langley posted “Setting the Record Straight: Statement on Flock Network Sharing, Use Cases, and Federal Cooperation” on June 19, 2025; smack-dab in the middle of CBP’s pilot program. Regardless, he assured his readers on the topic of federal access: “it is a local decision. Not my decision, and not Flock’s decision.”
Every city council gets the same pitch. Every council delivers it to constituents. The assurance that access is controlled, limited, and local is what gets the contracts signed. Three specific planks in the platform:
- Only your agency controls your data.
- Federal agencies do not have direct access.
- Nobody from Flock is accessing your footage.
None survive the paperwork.
The Campaign Trail
On February 26, 2025, at 10:47 PM Eastern, a Flock employee ran a search on Dunwoody, Georgia’s live surveillance network. The query was “chicken truck.” Then “cattle truck” — four more times. Then “lawnmower.”
The employee was Bob Carter, VP of Strategic Relations and Business Development at Flock Safety. He is not a police officer. He is a sales executive with a fully enabled search account on Dunwoody’s production network, with access to every camera in the Dunwoody sharing pool and far beyond.
Carter’s complete 2025 search record, read chronologically, is its own argument.
February 26, approaching midnight Eastern: “chicken truck,” then “cattle truck” four consecutive times, then “lawnmower.” Thirteen networks each. No case number.
By June 23: “white racecar with black stripes,” “potatoe chip van” (his spelling, verbatim), “ice cream truck,” “unicycle,” “rocket car.” The misspelling is Carter’s own — Dan Quayle’s ghost, haunting a live surveillance system. A rocket car does not exist in civilian traffic.
Carter kept returning to the unicycle through July and into the fall, workshopping the same searches like a candidate who can’t land a stump speech. By August he’d escalated to 892-network lookups — taking a locally-spotted vehicle and running it against the entire Flock network. In September, a blue Honda sedan toggled four times between a 13-network search and an 892-network sweep. By October, he’d moved from vehicles to people: “person on skateboard,” “person wearing orange vest and construction hat,” and the same yellow racecar searched three times in under an hour.
By December 9: “flatbed truck with lawn equipment,” “usps truck,” “ups truck,” “fedex truck.”
While Carter was busy maybe tracking his package, his colleague, Flock SVP Chris Colwell, sent out an email blast to Flock customers announcing that officer names, license plates searched, and open-text search reasons were henceforth removed from audit logs.
No longer would we be able to see Flock employees tracking their Amazon packages.
Carter’s March 4 session set his personal record: two consecutive lookups sweeping 6,350 camera networks simultaneously. While we will never know what fever dream of unicycles and race cars is on a loop in Carter’s mind, Flock will no longer let agencies across the country — from Virginia to Washington — know that a Flock VP searched “their” data for “SIZ3850” — which, according to lookupaplate.com, isn’t even a unicycle or a Honda.
There will no longer be reasons, names, or case numbers to keep an eye on Flock executives running midnight nationwide searches for rocket cars and unicycles on a national surveillance network.
This is what “Nobody from Flock Safety is accessing or monitoring your footage” looks like in practice.
The Rest of the Ticket
Because no good trip is taken solo, Carter was not running alone. Several Flock employees were created on Dunwoody’s account and given access as if they were Dunwoody police officers and command staff. In other departments’ logs, their searches appear as Dunwoody PD’s.
A February 2026 user export shows six Flock employees holding Owner-level access, equivalent to a department administrator. This grants them full control over search, cameras, users, and hotlists.
| Name | Role at Flock Safety | Flock Level | Searches |
|---|---|---|---|
| Bob Carter | VP, Strategic Relations & Business Development | Member | 401+ |
| Peter Barty | Staff Engineer, ML | Owner | ~27 |
| Kathleen Graham | NOVA Specialist | Member | ~11 |
| Amanda Bruner | NOVA Onboarding Specialist | — | ~5 |
| Randy Gluck | Manager, BD — 911/Emergency | Operator | ~1 |
| Bailey Quintrell | Chief Product Officer | Owner | — |
| Cam Whiteman | Principal Product Manager | Owner | — |
| Cory Charpentier | Senior Data Engineer | Owner | — |
| Martin Howley | Nova Product Lead | Owner | — |
| Jeff La Barge | Director of Product | Owner | — |
| Adam Snow | Director of Growth | Operator | — |
| Myron Maret | Customer Success Technologist | Operator | — |
Across 2025, Flock’s accounts generated hundreds of searches of Dunwoody’s network. Another Flock entity — Lucidus Tech API — is a programmatic API account tied to a Flock acquisition; Flock’s computer ran an additional 132 searches between January and March. Another API User (Forcemetrics) performed a single search in September 2025. Dunwoody at times appears more like Flock’s personal software lab than a functional police department.
The supporting cast is worth a glance. Amanda Bruner (Nova Onboarding Specialist): 5 searches of the same Georgia license plate over ten weeks, each sweeping between 887 and 891 agencies. No case number. An onboarding employee tracking a specific vehicle for two and a half months. Kathleen Graham (Nova Specialist): 11 searches of the same plate over three days, each across 888 networks. One at 11:40 PM. Randy Gluck (Manager, BD — 911/Emergency): 1 blank search — no query term, sweeping 898 networks. Peter Barty (Staff Engineer, ML): 27 searches, including one for a “Black Mercedes GL450 4MATIC” across 45 networks.
Whether this is stalking or development work is irrelevant to the overall point: these are Flock employees — and in some cases, likely not even that because Flock had not finished its acquisition of Lucidus in January — accessing a live ostensibly “law enforcement only” network handling federally-protected data from databases like NCIC.
And then there is Flock Intelligence. This is an unidentified operator that made 606 searches of Dunwoody’s network over five months, with identity, search filters, and case numbers fully redacted in the audit log. It appears alongside several other explicitly Flock-internal organizations in network logs (e.g., “Flock Safety - Admins,” “Flock Safety - Engineering”).
Most Flock Intelligence queries used the AI-powered freeform search. Some show patterns consistent with ongoing vehicle tracking; others searched for political expression — vehicles with Trump bumper stickers, “don’t tread on me” flags. Peter Barty’s Mercedes also appears as a Flock Intelligence query, suggesting “Flock Intelligence” may be a test account the Nova team uses to search live data.
Flock Intelligence is a separate entity not found in Dunwoody PD’s internal department logs: it shows up only in network-level audits, meaning that since the December changes, neither Dunwoody nor anyone else has any visibility into these searches as they are happening. The named employees in Dunwoody’s account entered through Dunwoody’s front door. Flock Intelligence came in through the side.
Flock’s FAQ is unequivocal: “Nobody from Flock Safety is accessing or monitoring your footage.” The audit log shows this to be false hundreds of times and on multiple levels.
The searches were audited — which is how we know about the unicycles and the race cars — but the claim was not that access is audited. The claim was that it does not happen.
The Backroom
The audit logs document the front door and the side door. A Loom training video documents the back door.
The video, titled Managing Data Sharing and User Access in Your Account, was recorded by Gaby Mahoney, Regional Customer Success Manager at Flock Safety. It was made as a customer tutorial. Rather than use a demo environment, she recorded it using the live national network that’s tracking all of us.
@vManaging Data Sharing and User Access in Your Account — Gaby Mahoney, Flock Safety CSM
Mahoney’s second sentence, verbatim:
So when I log into your account and go under the sharing tab, we can see that you still have one-on-one sharing with some agencies.
When I log into your account. Not “when you log in.” She logs in. Her credentials. Someone else’s account.
The address she visits is sharing.flocksafety.com/networkSharing — a live production URL, not a
demo environment — and the selected organization is Olympia WA PD.
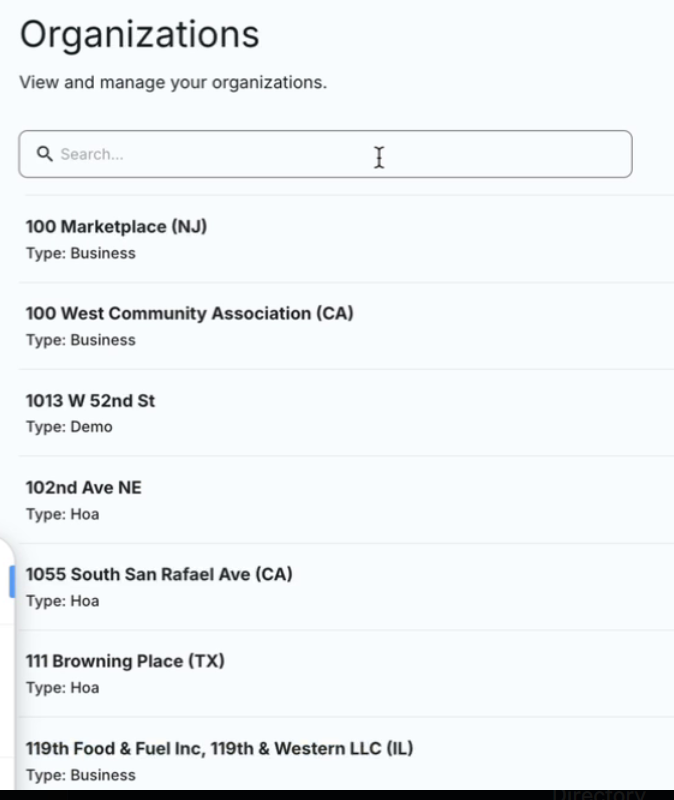
At the one-minute mark, she moves to users.flocksafety.com/organizations. This endpoint
(“organizations” — plural) most likely does not exist for Flock customers. Assuming Flock follows
even remotely typical SaaS patterns — which, to be fair, may be a bold and overly-optimistic
assumption — agencies would use a singular “organization” endpoint where they can see their own
admin panel and nothing else.
The video confirms the endpoint’s “staff-only” status by appearing to enumerate every customer in Flock’s system. Police agencies, HOAs, businesses, and residential users in multiple states all appear on Gaby’s screen as she types “Olympia” into the single searchable list.
She navigates directly into Olympia WA PD’s admin panel where her account surfaces the full administrative interface: Profile. Organizations List. Organization. Devices. Roles. Users. Zones. Authorized Access List. Transparency Portal. Integrations. Alerts & FlockOS. Billing. Contact Directory.
The Users tab shows Olympia WA PD’s sworn personnel — names, roles, last login dates, permission flags. Two entries carry “Flock” (rather than “External”) as the identity provider. These would not be subject to Olympia’s centrally-managed controls (like multi-factor authentication or automatic account deactivation at the end of employment).
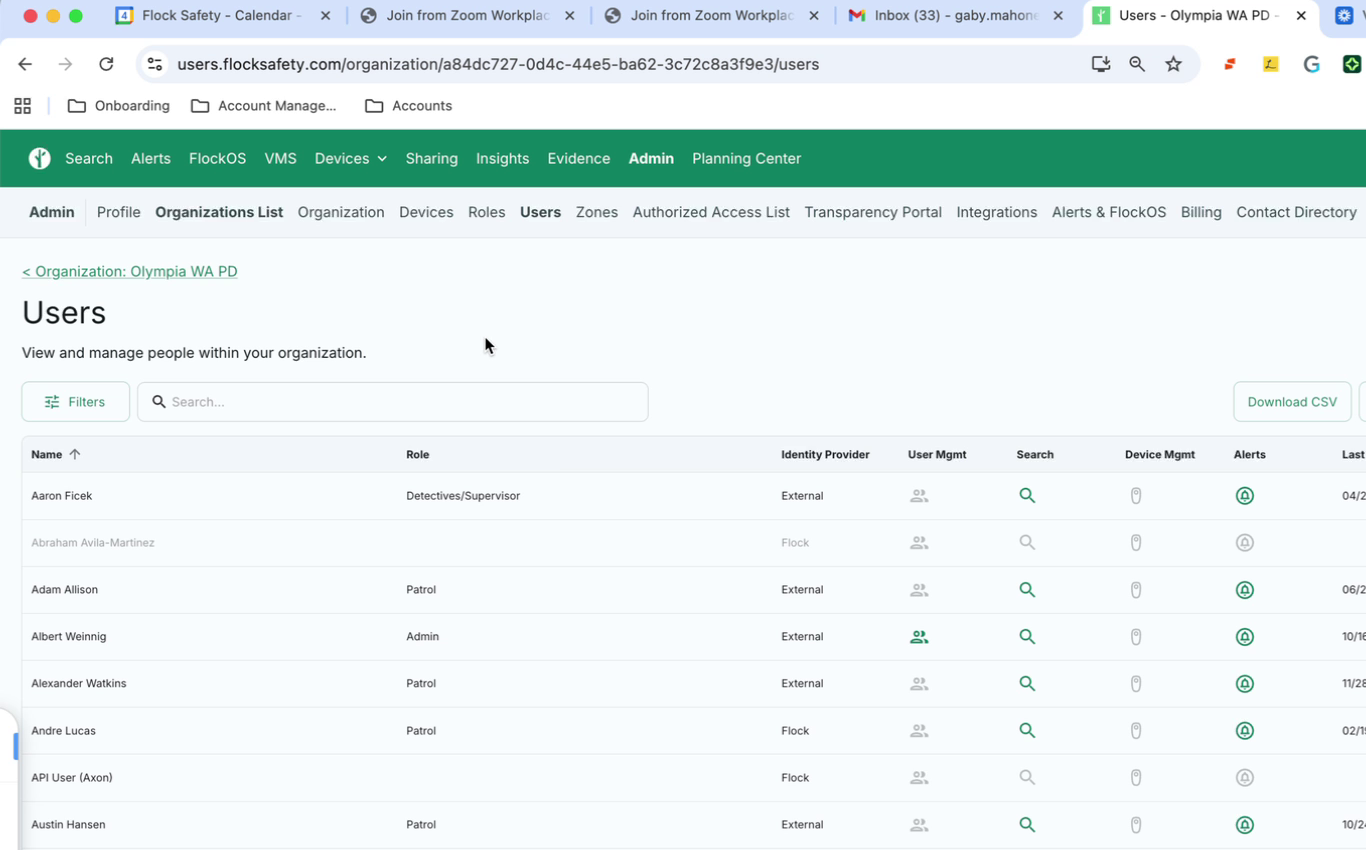
The network sharing panel shows Olympia WA PD’s “Shared with me” list: every Washington state agency sharing into Olympia’s network. Full permission sets for each. At the top of the screen is a red “Revoke Out-of-State Sharing” button next to the page selector, showing 107 rows in the “Shared Networks” table. Next to Aberdeen WA PD, a red button is shown:
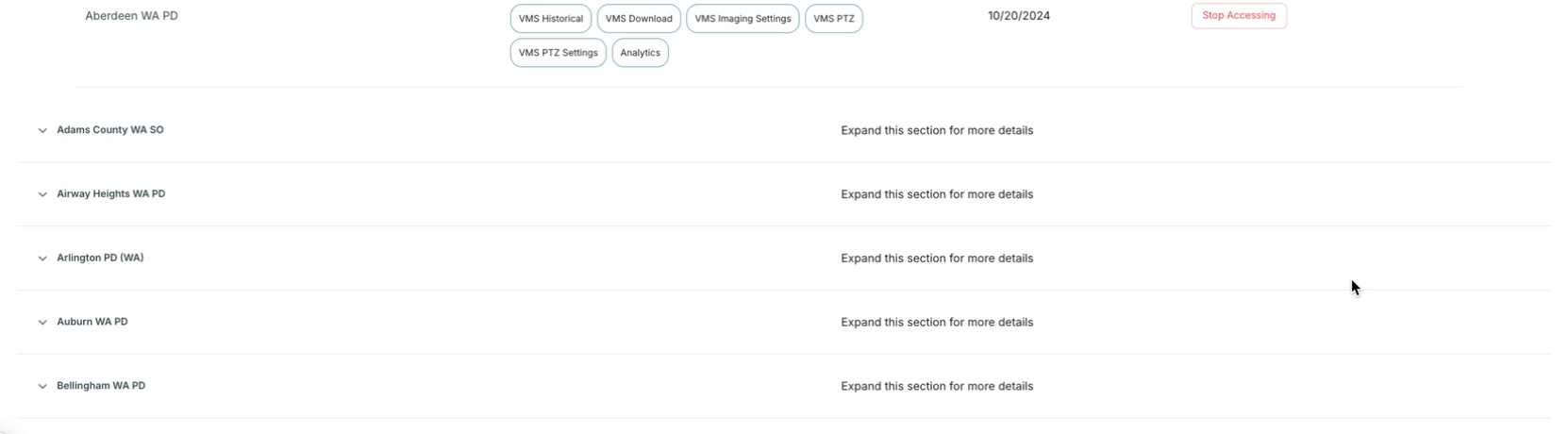
Mahoney’s account does not merely view Olympia’s configuration. The interface presents a live control to terminate the data-sharing relationship between agencies — unilaterally, without the knowledge or consent of the agencies.
It’s not only Flock’s CEO who can establish pilot programs while denying they exist, or Flock’s VP that can search for rocket cars. Even its customer service reps have administrator access.
“Only your agency decides who to share data with, not Flock.”
Redaction Day
The Mahoney video is the Rosetta Stone for what happened next. It shows that Flock staff — even its service reps and its sales execs — have high-level access to a live, national surveillance network. They can view, edit, or delete configurations. The CSM who can click Stop Accessing on any agency’s sharing relationship is the same person who walks agencies through narrowing their own exposure. That access is the precondition for everything that followed.
It’s worth noting what the video is actually for: Mahoney is guiding Olympia — a Washington state agency — through the process of restricting its sharing. Revoking out-of-state access, checking who can search its cameras, deactivating users. Near the end she says, “I also notice that you’re not enabled for the statewide or national lookup so that will be good in terms of auditing purposes.”
Limited access makes auditing easier. She knows what the inverse implies.
Five days after she posted the video, on December 9, while Carter was looking for his leaf blower, Flock SVP Chris Colwell sent an email to customer agencies titled “What you Need to Know About Recent Online Disclosures.”
That email announced that audit logs would be stripped of officer names, license plates searched, vehicle fingerprints, and open-text search reasons — framed as protecting active investigations and officer safety. Flock did not merely stop recording these fields going forward — it also retroactively replaced unique officer identifiers in its public Transparency Portals with the word “REDACTED.” The prospective removal ensures new searches go unattributed; the retroactive scrubbing rewrites the record of searches already conducted.
In the same email, Colwell recommended that agencies do exactly what Mahoney showed Olympia would “be good in terms of auditing purposes:” restrict sharing.
Reviewing your sharing settings and considering a temporary shift from Nationwide Lookup to Statewide Lookup.
He linked to an instructional video on how to do it.
Two days later, an FBI Supervisory Special Agent in Atlanta’s C9 Gang division forwarded the Houston HIDTA Officer Safety Bulletin to the broader intelligence community.
The bulletin described this site by name and recommended that agencies “ensure that their agency Flock settings have limited searches to sharing within state only or exclude the states/agencies that release their audit logs.” It further recommended that officers “ensure that the reason for the query be as vague as permissible (e.g., ‘Investigation’).”
Washington was named as one of the states from which FOIA-obtained audit logs had originated. The FBI was distributing instructions to help agencies evade the public records process — and one of its own field divisions was simultaneously using Flock data to prosecute federal cases.
It was a busy period. Houston HIDTA authored the bulletin, ROCIC — one of the RISS centers documented elsewhere on this site as carrying direct Flock database access — distributed it to law enforcement coordinators on December 10, and the FBI’s Atlanta office forwarded it on December 11. At approximately the same time, Flock implemented a blanket VPN block for all public transparency portals — which it holds out to be public accountability tools. A week later, Cyble, a Flock-affiliated firm, filed false abuse reports with Cloudflare in an attempt to take this site offline.
That is the service Flock was providing in December 2025: helping agencies make their surveillance data harder to audit while simultaneously stripping the audit logs of meaningful content, blocking anonymous access to public records, and attempting to silence the publication that had prompted the transparency requests in the first place.
And Carter stopped looking for unicycles and racecars.
The Candidate
On December 18, 2025, an affidavit in support of a criminal complaint was filed in the Southern District of Texas, Case No. 4:25-mj-770.
@Criminal Complaint — Case 4:25-mj-770
The affiant, Ryan Hilz, states under oath that he personally searched the Flock system. In ¶5: “Affiant also searched the Hyundai’s license plate through the FLOCK Safety System, from approximately November 15, 2025 12:00am through 9:00am.” He names a specific camera — “DB15 – Collingsworth (WB) from Broyles” — and narrows it to a two-minute window, 6:33am to 6:35am. In ¶6: “Affiant searched the Cadillac’s license plate through the FLOCK Safety System.” In ¶12, he reviewed Flock images from November 8 showing both vehicles parked side by side. He is not describing results handed to him by a colleague. He is describing searches he ran, cameras he queried by name, and images he personally reviewed.
The audit logs don’t show these searches. Between November 1 and December 1, 2025, the Hyundai plate (WFV2638) was searched 81 times in the Flock system — by Houston PD officers, Harris County Constable deputies, and two Harris County Sheriff’s Office users (V. Pag and m. bar). The Cadillac plate (WSF6471) was searched 86 times, again by Houston PD and Constable personnel, plus a handful of HCSO entries logged only as “C.” — a single initial with no last name. Harris County Sheriff’s Office does have a user account matching Hilz: “R. Hil.” That account’s last recorded search was May 16, 2025 — six months before the robbery. It does not appear in either plate’s November search history.
Hilz swears he searched — literally, swears, on penalty of perjury. The cameras he names are in the Houston network where 167 other searches by other officers are logged. There is an “R. Hil” with the Harris County TX Sheriff’s Office, but that account went dormant months earlier. Either he searched under someone else’s credentials — which means the audit trail attributes his work to a different officer, defeating the purpose of individual accounts and probably violating several federal regulations — or he accessed Flock through a pathway that doesn’t generate the same audit record, which means there are doors into the system that the logs don’t cover.
That gap matters because of who Hilz is. A federal Task Force Officer (TFO) is a state or local employee — a sheriff’s deputy, a city cop — assigned to work under a federal agency, usually through a formal agreement like the FBI’s Violent Crime Task Forces or ICE’s 287(g) program. The TFO keeps their local paycheck and local credentials, possibly including any Flock accounts tied to their home agency. But TFOs report to a federal supervisor, work out of a federal field office, investigate federal crimes, and file in federal court. The local credentials are what make TFOs valuable to the feds — they bring access that the federal agency could not get on its own. This is what Flock means when it says the feds don’t have “direct” access.
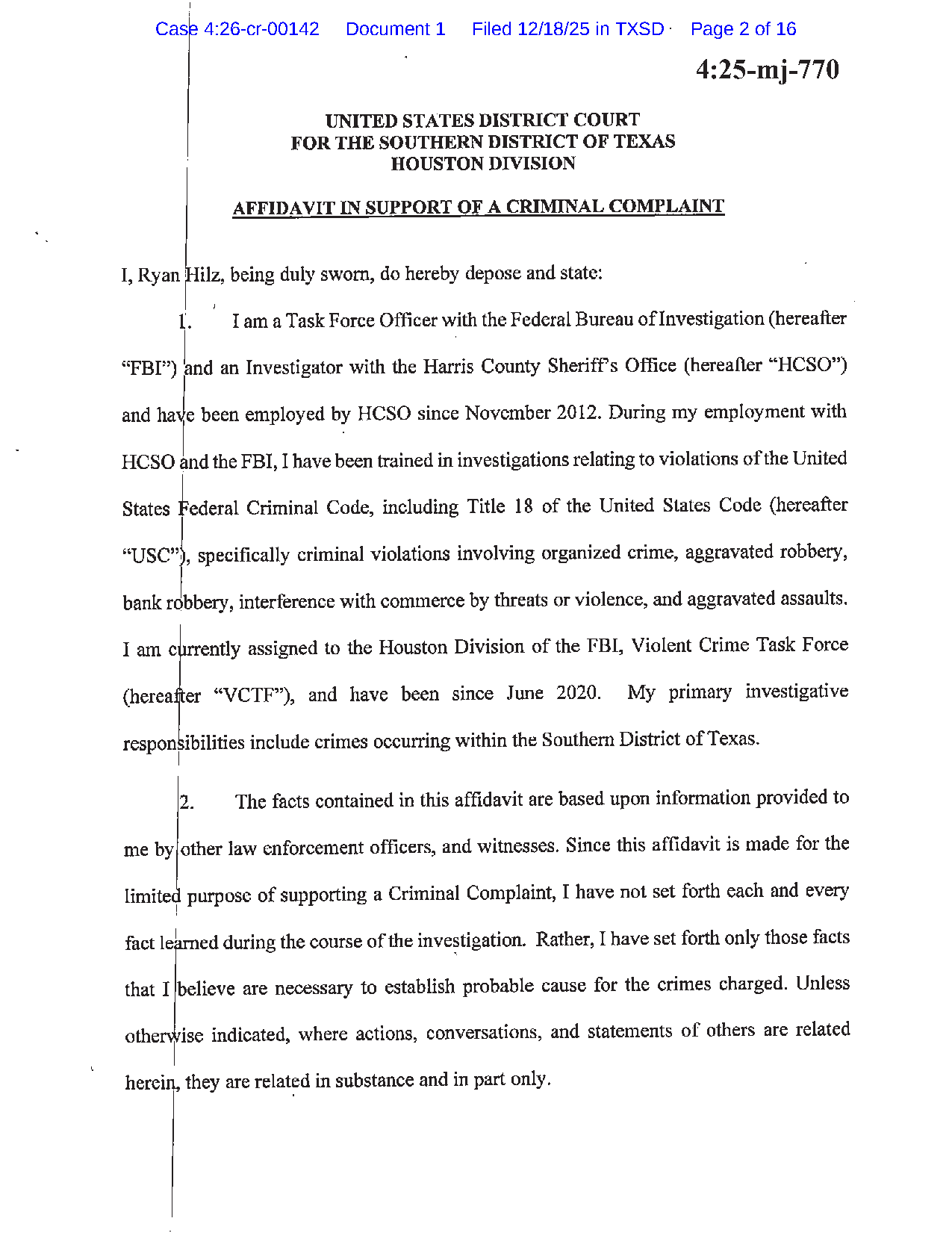
The first paragraph of Hilz’s affidavit:
I am a Task Force Officer with the Federal Bureau of Investigation (hereafter “FBI”) and an Investigator with the Harris County Sheriff’s Office (hereafter “HCSO”) and have been employed by HCSO since November 2012. During my employment with HCSO and the FBI, I have been trained in investigations relating to violations of the United States Federal Criminal Code […] I am currently assigned to the Houston Division of the FBI, Violent Crime Task Force (hereafter “VCTF”), and have been since June 2020. My primary investigative responsibilities include crimes occurring within the Southern District of Texas.
Read that introduction the way you’d read a candidate’s bio on a campaign flyer. His actual employer is HCSO — “employed by HCSO since November 2012,” buried mid-paragraph. But that is not the lead. His opening words: “a Task Force Officer with the Federal Bureau of Investigation.” FBI first. HCSO second. The phrase “during my employment with HCSO and the FBI” frames both agencies as concurrent employers — not a county deputy on loan, but a man who works for the FBI and also, incidentally, receives a paycheck from Harris County.
But maybe Hilz took a creative writing class and “Affiant searched” is not to be interpreted literally; his may be a sworn statement that sacrifices accuracy for brevity, the testimonial equivalent of “close enough for government work.”
But whether Hilz is committing some light perjury, whether Flock is misleading its customers about its relationship with the feds, or whether “no direct access” in a system riddled with Flock employee and TFO backdoors is the very best Flock can do: Langley unequivocally broke his campaign promise that it would be a local decision.
After “Hilz’s” Flock searches, the three suspects were transported to the FBI Houston Field Office for interviews (¶26). Inside that field office, one of them was shown a Flock image of the Hyundai and a Flock image of the Cadillac CTS (¶29).
An officer introducing himself as “a Task Force Officer with the [FBI]” showed Flock surveillance images to a suspect in a federal criminal case, while he was being held by federal agents in an FBI interrogation room in a federal building.
To dispel any remaining ambiguity about whether this was local, look to the signature block:
Ryan Hilz Task Force Officer Federal Bureau of Investigations
He signed as FBI — not HCSO. The only thing that supports that he might not actually be a fed is that he misspelled the name of the agency he spent 16 pages claiming to work for. There is only one “Investigation” in the Federal Bureau of Investigation.
The federal government’s sworn affiant lifts the veil on Flock’s empty promises: the federal government has access, no matter how you spell it.
Flock’s own timeline confirms the infrastructure that made this possible. Its blog states that the federal “pilot” program with the FBI concluded in 2023, and that “[i]n August of 2025, Flock publicly announced it would no longer conduct pilot projects with federal agencies.” The “try” part was cancelled; the “buy” part was not. The FBI does not respond to FOIA requests about Flock. Langley’s “Setting the Record Straight” post, published June 2025, assured readers that federal access was “a local decision” — while the CBP pilot he disclosed in January 2026 was actively running.
The Fine Print
The federal-access issue draws the most attention at council meetings, but the “sworn law enforcement only” claim — which directly supports Flock’s assurance that “Nobody from Flock Safety is accessing or monitoring your footage” — fails even within the agencies that own the accounts.
| Name | Role | Flock Level |
|---|---|---|
| Adria Crum | Records Supervisor / Property & Evidence Tech | Owner |
| Sybil Fisher | Police Crime Scene Technician | Owner |
| KC Tate | Property & Evidence Technician | Owner |
| Kayce Lowe | Crime & Intelligence Analyst | Owner |
| Kimberly Stone | Police Service Representative | Owner |
| Skylar Lewis | Public Safety Ambassador | Operator |
| Eric Ziglin | Public Safety Ambassador | Member |
| Paul Chastain | Public Safety Ambassador | Operator |
The pattern extends beyond individual agencies. The Regional Information Sharing Systems (RISS) — funded by DOJ, operated by regional centers incorporated as private nonprofits — is the task force model applied to data: federal money, non-government hands, Flock access.
Five of its six centers carry direct Flock database access through RISSIntel, a federated search tool that lets RISS analysts query Flock’s data without maintaining individual Flock accounts. ROCIC, the RISS center that distributed the Houston HIDTA bulletin instructing agencies to evade public records requests, is one of them. The National Center for Missing and Exploited Children (NCMEC) is named in Flock’s own LPR policy definition as a hotlist data source. NCMEC is a private organization. It populates the alerts that fire on your plate.
The ACLU/UIowa ALPR report documented the same pattern across Iowa: civilian analysts, support personnel, and non-law-enforcement government staff with active Flock accounts across dozens of agencies.
The CJIS Security Policy is explicit about what this requires. Section 5.12.1.2 mandates that all personnel with access to Criminal Justice Information — including private contractor employees — undergo fingerprint-based state and national background checks before access is granted. Section 5.1.1.5 requires that vendors sign the CJIS Security Addendum, which extends the full weight of CJIS security requirements to their staff. Sections AU-9 and AU-11, aligned with NIST 800-53, require that audit logs be protected from unauthorized modification and retained for at least one year. Flock’s December audit-log stripping, its employee access without documented screening, and its unilateral modification of log fields all appear to run afoul of these provisions.
When Story County, Iowa requested Flock’s CJIS certification list, Flock produced 28 names — all with first names starting A through C, several illegible — and no one else. No installers, no subcontractors, no overseas workers, and none of the employees running Flock’s own sales and training accounts on production data. The list is the compliance equivalent of Carter’s searches: performance art.
The contracts themselves offer no backstop. Flock has moved its terms of service to a web URL it controls unilaterally and can change without customer notice. It requested that archive.org’s Wayback Machine exclude its website, preventing any historical record of the terms as they existed when a city signed them. The new terms strip data ownership from agencies and supersede all prior agreements upon any subsequent order — even a camera repair.
No policy implements the “sworn only” promise, no mechanism exists to enforce it, and the contracts are written to ensure that no one can prove what they originally said. “Access is limited to sworn law enforcement” is, at best, wishful thinking.
The Town Hall
When Dunwoody’s Flock contract came up for approval, the council heard the stump speech: access controlled, limited, and local. Only your officers. Only for investigations. Only under oversight. The Dunwoody City Council held its regular meeting on March 23, 2026. As part of its discussion of the Dunwoody Flock contract, an “audit” — if we use the term loosely — would be delivered.
@Dunwoody Flock Audit (Council Meeting Presentation) — March 23, 2026
The audit included a FAQ slide with question 3: “Who can access the data, and how do you prevent misuse?” The city’s answer: “Access is limited to authorized, trained personnel who need it to perform official duties.” The people who wrote that sentence had the audit log that showed a Flock employee was using Dunwoody’s account to look for unicycles and race cars.
Flock Safety even sent its chief legal officer, Dan Haley, to address concerns from the public. A resident had already recited the numbers before Haley took the floor: 401 searches by Flock employees, Owner-level access, live drone footage and hotlist control. Haley addressed none of it.
Haley spoke about machine learning training data — de-identified images, less than 1%, used to improve plate-read accuracy. The city’s own attorney called the data-use provision a loophole and said it could be closed in the new contract being negotiated. Haley corrected her on-mic: “It’s not a loophole, it’s for system quality and improvement.” It wasn’t a question anyone had asked — not even the FAQ.
The council member who asked “It seems like Flock staff has access to our footage. Is that true?” got an answer about plate-design recognition models, but the real question, why a VP of Business Development was searching for “potatoe chip van” on a live police network, went unasked by the council or the city staff who “audited” Flock. Haley certainly did not volunteer an answer.
The Dunwoody police chief did confirm that Flock engineers had been inside the system “under agreement” for integration and testing. There were no immediate objections from the dais to a commercial company using city residents as surveilled guinea pigs — nor, for that matter, to its marketing team using Dunwoody PD to shoot commercials.
The Endorsement
Dunwoody’s Technology Director’s written assessment — submitted to council alongside the FAQ — concluded that the risks of continued Flock use are “acceptable,” in part because “the users accessing the data are law enforcement meeting CJIS standards.”
The same assessment scored “Non-PD direct logins” as a Yellow risk — a documented, acknowledged problem that undercuts the memo’s overall conclusion, which rests on the premise that only law enforcement has access.
The full security assessment matrix tells an even worse story.
@Dunwoody Flock Security Assessment Matrix
All six vendor remote access control items — “Vendor remote access controls,” “MFA enforcement,” “PAM (JIT, vaulting, break-glass, recording),” “Provisioning/deprovisioning,” “Credential storage/password policy,” and “No backdoor accounts” — were rated Green.
That would be good, except the supporting evidence column for every one of them: no evidence. For “No backdoor accounts,” the assessor specifically requested a written attestation from Flock’s security leadership. It was “not specifically provided as requested.” Green anyway; we have apparently entered a new era of vibe-based auditing and compliance.
Item Q4.6 asked whether Flock had made audit log field reductions since October 1, 2025. The answer: none. The rating: Green. The assessment was prepared for the March 23, 2026 council meeting — more than three months after Flock’s December 9, 2025, mass email blast to its customers announcing that officer names, license plates searched, vehicle fingerprints, and open-text search reasons were being removed.
The only item on the matrix rated Red was Q8.1: breach/security incident history. Flock told the assessor it had no breaches in the past three years. The assessor noted that “camera breaches have been highly publicized and should have been mentioned at a minimum (December 2025).” Even the assessor could see that one. It probably would have been hard to deny when Benn Jordan, the security researcher who made the video that exposed the problem, spoke at the start of the meeting.
The Mahoney video shows what no-evidence Green looks like from the inside.
After more than an hour of public comment and questioning, the council voted unanimously to defer the Flock 911 contract to the April 13th meeting, pending completion of a new master service agreement. The motion was made by Stacey Harris, seconded by Rob Price. No one voted against deferral. No one voted to cancel.
The Moment
The reality is that non-sworn city staff have access. As do Flock employees. As does the FBI.
Flock’s standard response to this kind of reality check is to observe that employee access is technically logged, that TFO searches are formally local-agency queries, and that civilian staff access is controlled by the agency rather than Flock. Even if that were all true, it’s a description, not a solution.
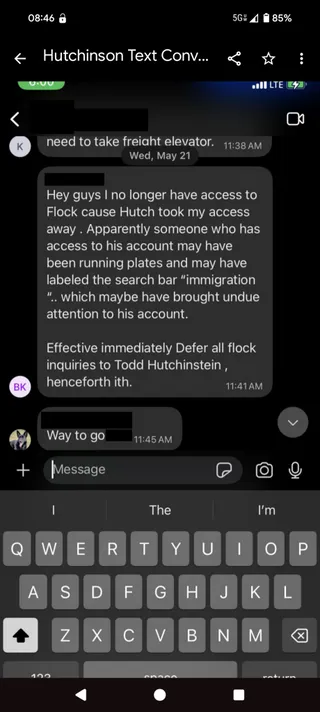
The people doing the account sharing don’t even know who does what searches; they consider getting caught “undue attention” rather than a violation of federal security regulations and professional standards. A November 2025 letter from Senator Wyden of Oregon says his staffers were able to find Flock accounts for sale.
As a custodian of billions of data points on hundreds of millions of people, Flock should be trying to prevent these problems, but instead it actively engineers them. Its public position is that of the passive service provider in an imaginary world where local governments are in the driver’s seat.
In private, Flock employees are placed on police department rosters, so that a VP’s search for rocket cars is attributed to the department, not Flock. Then it strips the audit fields that would let officials detect the difference.
This analysis looked at a single, relatively small police department. There are tens of thousands of users with law enforcement level access across 6,000+ departments, and hundreds, possibly thousands, of those users were never vetted by anyone. Dunwoody deferred the vote. Other cities will face the same choice. All that elected officials have to do is read the paperwork.
We don’t need to let Flock define “this challenging political moment.” We can vote them out.